Thunder CTF allows players to practice attacking vulnerable cloud projects on Google Cloud Platform (GCP). In each level, players are tasked with exploiting a cloud deployment to find a "secret" integer stored within it. Key to the CTF is a progressive set of hints that can be used by players when they are stuck so that levels can be solved by players of all levels from novices to experts.
Thunder CTF deploys level infrastructure on demand to a player's Google Cloud Platform project. Players new to Google Cloud can get a free $300 credit here. Thunder CTF is very cheap to run, with its resource consumption fitting almost entirely into GCP's free tier. To save cloud credits, we recommend deploying levels only while you are playing and destroying them as soon as levels are completed.
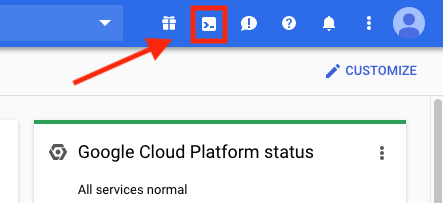
The CTF is played through Cloud Shell, a command line interface that is already set up for accessing cloud resources. It can be accessed by clicking on the Cloud Shell icon in the GCP console:
After creating a new project and enabling billing for it, open Cloud Shell and ensure that it points to the project you just created.
gcloud config set project [PROJECT-ID]
Then, create a Python virtual environment that will be used to launch the exercises.
virtualenv -v env-tctf source env-tctf/bin/activate
Then, clone the CTF and install its required packages
git clone https://github.com/Vincentmask/thunder-ctf.git cd thunder-ctf pip3 install -r requirements.txt
Then, enable the resource manager and service usage services for the project
gcloud services enable \
cloudresourcemanager.googleapis.com \
serviceusage.googleapis.com \
compute.googleapis.com \
appengine.googleapis.com
Then, in root directory, edit terraform.tfvars to fill in the project id
vim terraform.tfvars
Finally, initialize the project for the CTF by enabling all required services and logging features:
terraform init terraform apply -target=module.setup -auto-approve
If you want to do the defender path labs later, run the audit Logging module to turn on audit logging.
terraform apply -target=module.auditLogging -auto-approve
You are now ready to play the CTF!
Levels:
Level Development
Thunder CTF was built to be extensible, and we encourage players to make their own levels. For more information on how to create a level, visit the Level Development Guide and the Thunder CTF framework documentation.